When Does an Event Become a Security Threat?

To improve perimeter intrusion detection systems for critical infrastructure and high-value sites, let’s first consider the core elements that comprise a valid security threat. A security threat is, at its heart, the potential for an adversary to obtain unauthorized or unlawful access to a secured area or facility. For a crime to occur, three things need to happen at the same time (the “crime prevention triangle”): opportunity, means/ability, and motive.
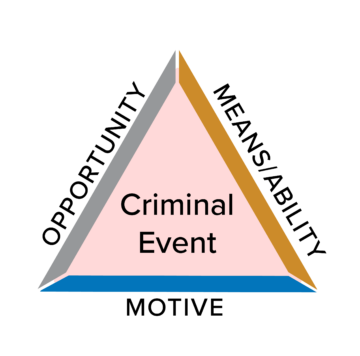
Through careful risk analysis and crime prevention by environmental design (CPTED), security professionals can target one or more sides of this triangle, greatly improving site security.
The opportunity aspect is hard to address; often the existence of the facility itself creates the opportunity. That being said, maintaining a locked down site, free of visible targets or obvious vulnerabilities, will help reduce risk.
The intruder’s ability to attack (means), is directly addressed via physical barriers, including locked doors, security fencing, walls, and anti-vehicle bollards/barriers. However, the popular saying “a fence only keeps honest people out” exists for a reason – a motivated intruder can cut, climb, or otherwise bypass a fence in seconds. In correctional or military environments, fences can be enhanced with razor wire or other physical deterrence mechanisms, but even these are still not enough defense against motived individuals, and for civilian environments, such measures are typically unfeasible or forbidden. As such, fences by themselves are not complete security solutions.
The third component, motive, is the one addressed by the majority of video surveillance and intrusion detection technologies. We might not know an intruder’s internal thoughts, but we can infer motive and take action based on their demonstrated actions, namely through the detection of unauthorized entry, followed by active assessment (and response when required).
The Need for Context When Inferring Motive
A potential weakness of intrusion detection technologies is a lack of full context when deciding if an event is generated by a real security threat or something that, from the perspective of the system itself, merely resembles it. We call them nuisance alarms for a reason – they distract security personnel, waste resources, and even lead to system mistrust and complacency. In the worst case, they may cause operators to ignore real threats. For these reasons, intrusion detection solutions need to be more than just an application of a given technology; rather, they need to be designed from manufacturers with experience in the field who understand the nature and context in which an event occurs.

Perimeter fences adjacent to public areas require new technological approaches to intrusion detection as the mere presence of individuals near the fence does not indicate an active threat.
For example, consider video analytics. By leveraging a site’s existing surveillance system, they provide a low-cost solution for automated intrusion detection. However, video lacks the full context of intrusion events – it is inherently two-dimensional and lacks “ground-zero” data, which can lead to poor performance in all-too-common situations:
- In less sophisticated analytic systems, insect movement on or near the camera can be mischaracterized as intrusion events further away, while wind shaking cameras and moving vegetation, can lead to invalid movement detections.
- Lawful nearby activity (for example, a person walking along a public sidewalk running parallel to the fence) can appear as an intrusion event, even if the person does not actually touch the fence.
- Vehicle headlights, flashlights and laser pointers can be used to overwhelm a camera’s sensor, enabling intrusions to go undetected.
- Poor visibility during extreme weather conditions like snowstorms, sandstorms, thick fog or heavy rain can wreak havoc on video quality and overall analytic performance, leading to false or (even worse) missed detections.
- Insufficient lighting can cause video analytics to be blind and not see relevant events.

Spiders, spider webs, and flying insects can degrade the effectiveness of some video analytic solutions.
Another approach to intrusion detection is fence-mounted sensors. Fence-mounted sensors are also highly cost-effective, as they leverage the fence itself for detection. One of their key strengths is that they interpret motive (intent) directly from the intruder’s actions; namely the intentional, non-natural disturbance of the fence fabric itself. Simply walking near a fence (e.g. a guard on perimeter patrol) does not trigger an alarm. The fence is a logical demarcation between lawful and unlawful activity, the “red line” for determining intent. However, as with video analytics, fence sensors lack the full security context (they provide fence disturbance data at one physical location), potentially resulting in a lower detection rate in specific intrusion edge cases.
Sensor Fusion: Context-Based Decisions
Senstar’s extensive experience and comprehensive portfolio provides it with the unique ability to offer innovative solutions that are not tied to or limited by any one technology. Senstar’s Sensor Fusion Engine is a unique, groundbreaking technology, that can defeat nuisance alarms once and for all while maintaining the highest Probability of Detection (PD).
The Sensor Fusion Engine uses context to intelligently infer motive and detect intruders. More than just a simple Boolean logic integration, the sensor fusion engine accesses low level data from both AI-enhanced video analytics and fence sensors to correctly characterize perimeter threats:
| Event | Sensor Fusion Engine Characterization |
| Regular fence climb | Security threat (intrusion detected) |
| Person near perimeter | No active threat (no intrusion alarm) |
| Person climbing, cutting, or lifting fence | Security threat (intrusion detected) |
| Insect on camera lens appearing to “climb” fence | No threat (no alarm) |
| Severe storm (winds, hail, rain, etc) | No threat (no alarm) |
| Loose fence signage or damaged fence fabric | No threat (no alarm) |
| Snowdrifts against the fence | No threat (no alarm) |
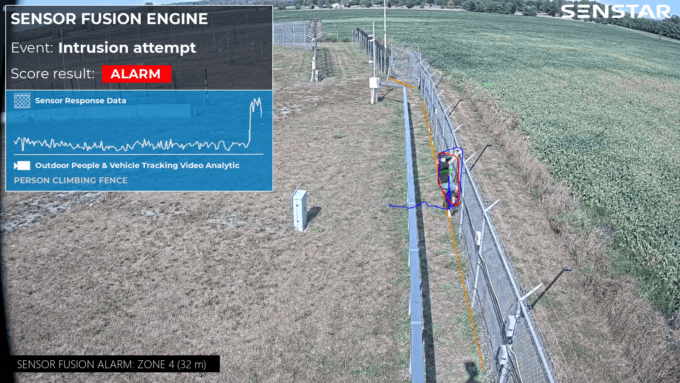
The Sensor Fusion Engine uses context to intelligently infer motive and detect intruders.
Enhancing Your Existing System
The Sensor Fusion Engine is licensed per-camera, meaning you can use it to protect an entire perimeter or to enhance specific perimeter segments that are either high-risk or prone to nuisance alarms. It can be deployed as a drop-in solution or as part of the full-featured Senstar Symphony Common Operating Platform:
- Drop-in solution – Pre-installed on a physical security appliance (PSA), the Sensor Fusion Engine generates zone alarms when valid intrusions are detected. The PSA communicates -with third-party Video or Security Management Systems (VMS/SMS) via SDK integrations, TCP/IP messages, or hardware I/O.
- Senstar Symphony video analytics – By adding fence sensors to the system, the precise intrusion location is displayed on a graphical map and the alarms can be used for camera call-up and to trigger customizable action sets via Senstar Symphony’s rules engine.
A Better Approach to Perimeter Security
To improve performance and avoid the limitations of individual technologies in specific edge cases, new approaches to intrusion detection are required. By understanding context, the Senstar Sensor Fusion Engine can differentiate between a benign event and real security threat. The Sensor Fusion Engine adds intelligence to a site’s security system, empowering security personnel by providing them with relevant and timely information about perimeter activity.
For More Information
For more information about how the Senstar Sensor Fusion Engine can improve security at your site, contact your local Senstar representative.