Advancing Technologies and Simplifying Deployment to Address Security Needs

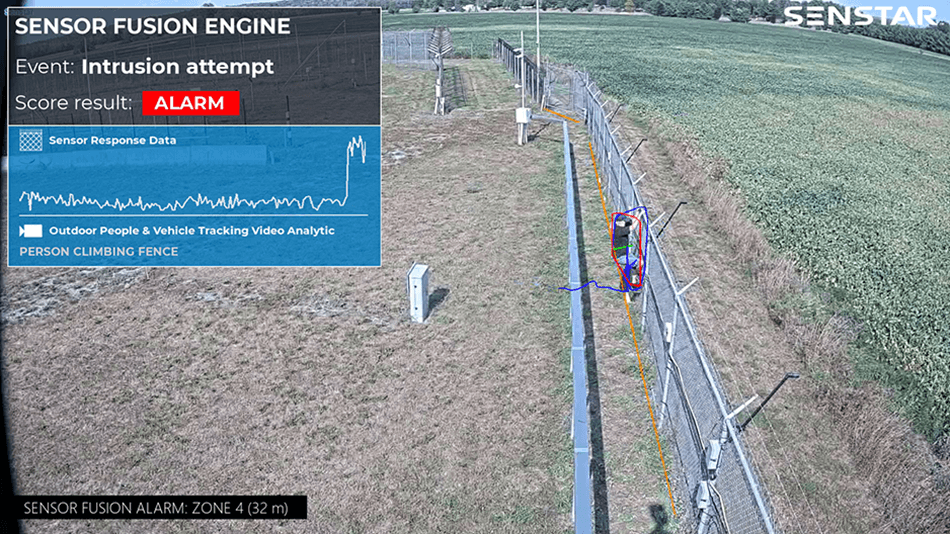
Senstar, with its broad portfolio of video management software, perimeter intrusion detection sensors, access control software, and intelligent video analytics, offers a range of innovative, flexible security solutions to assist operators in detecting, deterring, and responding to intrusions.
While Senstar products are protecting thousands of sites across the globe, there are four key markets the company is focusing on to advance technologies and simplify deployment – utilities (electrical, communications, and water), logistics, corrections and energy.
Electrical Utilities
Protect sites from intrusions and avoid liability.
Electrical utility assets are constantly at risk of attack, vandalism, and theft. There are also regulatory compliance concerns and the liability risk associated with trespassing.
Communications Utilities
Protect critical communications infrastructure.
Highly visible, unmanned and deployed in large numbers over long distances, cellular tower sites are at considerable risk for attack, vandalism, and theft. As well, data centers and related infrastructure, including buried datalines, require protection to ensure continuity of service.
Water Utilities
Protect infrastructure and keep water clean and safe.
To maintain clean, safe water, treatment plants, pumping stations, storage tanks, and reservoirs need to be secured and monitored for suspicious or unauthorized activity.
Logistics
Mitigate risk through security and business intelligence.
To avoid disruptions and maximize productivity, warehouse, fulfillment, and distribution facilities require solutions that reduce risk from both external and internal threats while providing insight into operations and business processes.
Corrections
Prevent escapes and keep staff safe.
Senstar has 40 years of experience working with correctional institutions to secure perimeters and keep staff safe. It offers products that are uniquely tailored for their challenging and potentially dangerous environments.
Energy
Protect above and below-ground infrastructure.
From initial extraction to end-point deliveries, the production chain relies on safe extraction, refining, and distribution across great distances. Pipelines and associated above-ground infrastructure along the chain are vulnerable to theft and sabotage.