Protect Your Data Center. Ensure Continuous Operations.

Data centers are the engine driving the digital economy—powering AI workloads, cloud computing platforms, and critical data storage that businesses and governments depend on 24/7. A single physical security breach can compromise sensitive data, disrupt services affecting thousands of users, and damage customer trust. Even seemingly minor incidents like unauthorized access, equipment tampering, or accidental damage to data lines can result in substantial financial losses when downtime, liability, and reputational damage are considered.
With over 40 years of experience securing critical infrastructure worldwide, Senstar provides field-proven solutions specifically designed to help data center operators protect mission-critical computing resources while meeting stringent security best practices and business requirements.
The Six Pillars of Data Center Physical Security:
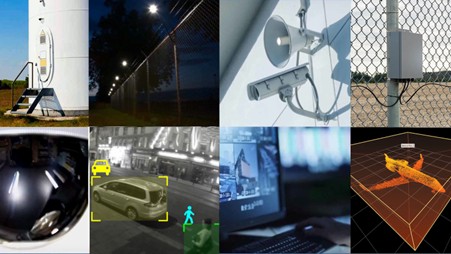
- DETER – Visible signage, perimeter security lighting, explicit surveillance, and automated warnings
- DETECT – High-performance perimeter intrusion detection, AI video analytics, LiDAR, and access monitoring technologies delivering the highest probability of detection with minimal nuisance alarms
- DELAY – High-quality security fencing, anti-vehicle bollards, and hardened building access points
- ASSESS – Precision target tracking, automated PTZ control, day/night/thermal cameras, and real-time event verification
- COMMUNICATE – Real-time alerts via email, SMS, and mobile apps with exact coordinates and video evidence
- RESPOND – Mobile support with accurate location data, integrated alarm management, and automated incident workflows
Conducting a Comprehensive Threat Assessment

A comprehensive threat assessment forms the foundation of an effective data center security strategy, enabling operators to identify vulnerabilities across three critical protection zones—facility perimeter, power infrastructure, and data connectivity—prioritize security investments, and implement targeted protection measures.
Understanding Multi-Layered Security Requirements
Effective data center security requires protecting against threats at every layer.
- Facility protection must address perimeter breaches, unauthorized building access, server room intrusions, and cabinet tampering.
- Power infrastructure security requires safeguarding outdoor electrical equipment, generators, battery backup systems, and HVAC units from vandalism and sabotage.
- Data connectivity protection demands monitoring buried fiber optic lines against accidental damage, deliberate tampering, and third-party interference that could sever critical communication pathways.
Common Threats and Vulnerabilities
Site security evaluations typically identify multiple threat scenarios including unauthorized access attempts, theft of high-value IT equipment, vandalism and sabotage, data theft from physical access to servers, vehicle ramming attacks, fence cutting/climbing, tailgating at access points, and damage to buried data lines from construction or deliberate interference. Beyond physical breaches, operators must also address operational threats such as unauthorized access to equipment cabinets, tampering with cooling systems, service interruptions affecting customer SLAs, fire and environmental hazards, and insider threats from employees or contractors.
Effective threat assessments require evaluating asset criticality (customer impact, revenue at risk), analyzing vulnerabilities in existing security measures, assessing threat probability based on location and threat landscape, calculating potential consequences including downtime costs and reputational damage, and incorporating third-party verification and penetration testing.
Adapting to Evolving Threats
Modern data centers face an increasingly sophisticated threat landscape. Security systems must adapt through regular reassessment cycles, scalable technology platforms supporting growth and new facilities, flexible sensor configurations for changing layouts, updatable analytics and detection algorithms leveraging AI advances, and integration capabilities for emerging technologies—ensuring your security posture remains effective as threats evolve and infrastructure expands.
How to Evaluate Physical Security Technologies
Selecting the right physical security technologies requires a systematic evaluation process that balances comprehensive protection requirements, operational efficiency, and long-term total cost of ownership.
Aligning Technology with Security Requirements
Not all security technologies are created equal. Successful deployments require careful evaluation of how each technology contributes to the six required functions: Deter, Detect, Delay, Assess, Communicate, and Respond. When evaluating physical security technologies for data centers, consider:
- Detection performance: >95% probability of detection with minimal nuisance alarm rates across perimeter, facility, and data line protection
- Assessment capabilities: precise location accuracy, target tracking, AI-powered classification distinguishing threats from routine activity)
- Integration and scalability: open protocols, multi-site management, compatibility with existing access control and building management systems)
- Operational reliability: MTBF, redundancy options, remote diagnostics, high availability architectures
- Environmental suitability: indoor/outdoor deployment flexibility, extreme temperature tolerance, EMI resistance near electrical equipment.
Making the Right Decision
A successful technology evaluation requires a clear requirements definition that maps technologies to specific protection zones and security functions, a total cost of ownership (TCO) analysis (equipment costs, installation expenses, and 10-year operational costs including reduced false alarms and truck rolls), vendor expertise with proven data center experience, long-term technical support availability with rapid response SLAs, and a future-proof architecture ensuring solutions scale with facility expansion and technology evolution.
Before full deployment, conduct site surveys across all protection zones, perform pilot installations testing detection accuracy and integration, measure baseline performance and nuisance alarm rates, validate integration with VMS and access control systems, and train security and operations teams to ensure maximum effectiveness and rapid incident response.
Download Senstar’s Data Center Security Guide
Our comprehensive Physical Security for Data Centers Guide includes:
- Multi-layered security framework for facility, power, and connectivity protection
- Sample site with threat-specific detection strategies
- Deployment and integration considerations
Complete this form to download Senstar’s free guide now and discover how Senstar can help secure your data center physical infrastructure.
